Service Accounts
Service accounts allow Data Service Admins to create service accounts with access keys that have an extended lifetime and can be used to integrate with 3rd party tools.
A common use case is allowing users to integrate their notebooks (e.g. Jupyter, Zeppelin), BI tools (e.g Tableau) or other 3rd party services to access Ascend on the user's behalf without using the user's credentials to do so. In this way, users can grant access to multiple 3rd parties and manage them separately. The pattern follows how cloud providers allow administrators to create service accounts and assign them keys.
Service Accounts tie to one particular Data Service and do not expire.
Credential Types
There are two distinct credential types:
- Access Key ID + Secret - Used for applications that require both an access key and secret (e.g., File-Based Access, Python SDK, etc.)
- API Token - Used for web-based access or username / password access (e.g., Tableau)
Credentials are only viewable once when generated and cannot be modified or viewed again after that. New credentials can be generated and added to a Service Account at any time.
Service Account Permissions
| Permission Name | Permissions |
|---|---|
| No Access | Disables the account |
| Data Feed Read Only | Allows access to Data Feed(s) only. No access to other components (i.e. read/write connectors and transforms) or the Data Service. Typically used with BI Tools like Tableau. |
| Read Only | Allows read access to all connectors, transforms, and data feeds. Also allows read access to data service information and data flow information. Typically used with notebooks (Jupyter, Zeppelin). |
| Full Access | Allows read and write access to all aspects of Components, Dataflows, and the Data Service. Typically used with CI/CD systems to automate management and deployment of Dataflows. |
Permissions Required to Manage Service Accounts
- A Data Service's User Admins can create / delete a Service Account and create / delete access keys for a Service Account
- A Data Service's User Admin can change the permissions of a Service Account.
- Data Service Team members who are not User Admin can see the list of Service Accounts, but cannot create, edit, or delete them.
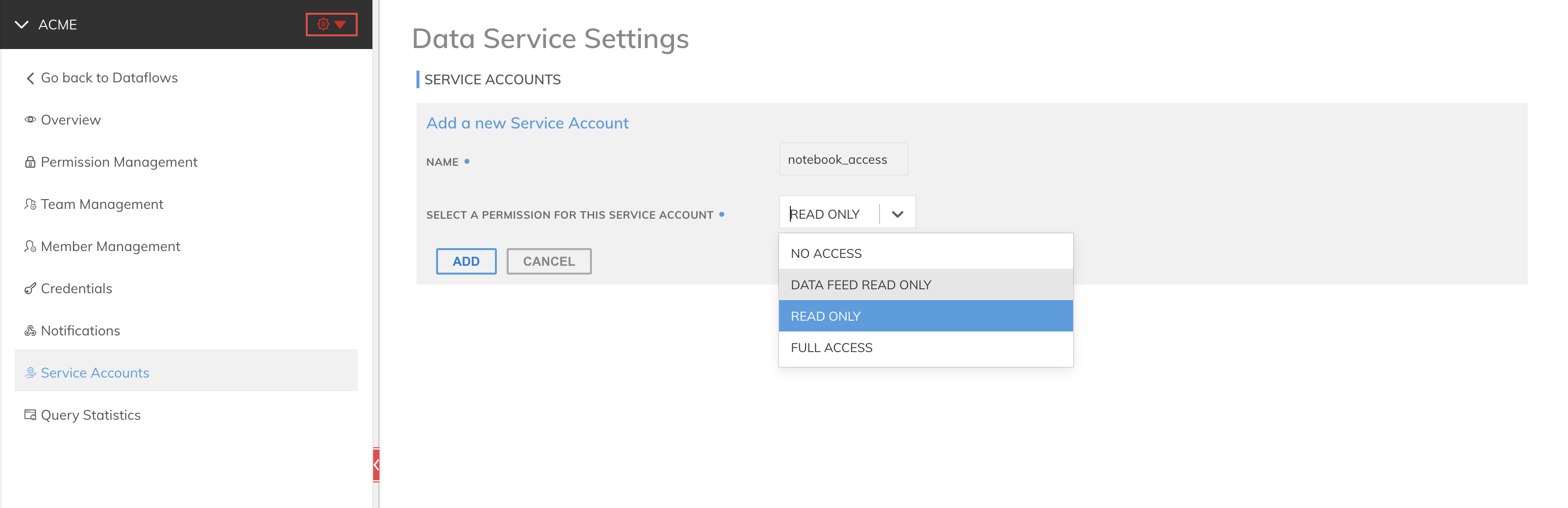
Creating Service Accounts and Access Keys
- Service accounts are managed from the Data Service Settings
- Select the Service Accounts tab.
- Click Add New Service Account button and enter a name.
- Select a Permission for this service account
- Click the ADD button to create the account.
Create Access Key with "Access Key ID + Secret" Credential Type
- Locate the Service Account in the Service Accounts tab.
- Click the + ACCESS KEY button in the drop-down
- A pop-up window displaying both the Access Key ID and Secret Access Key will be presented. This is the only opportunity to copy the secret access key. You may, however, create new access keys at any time.
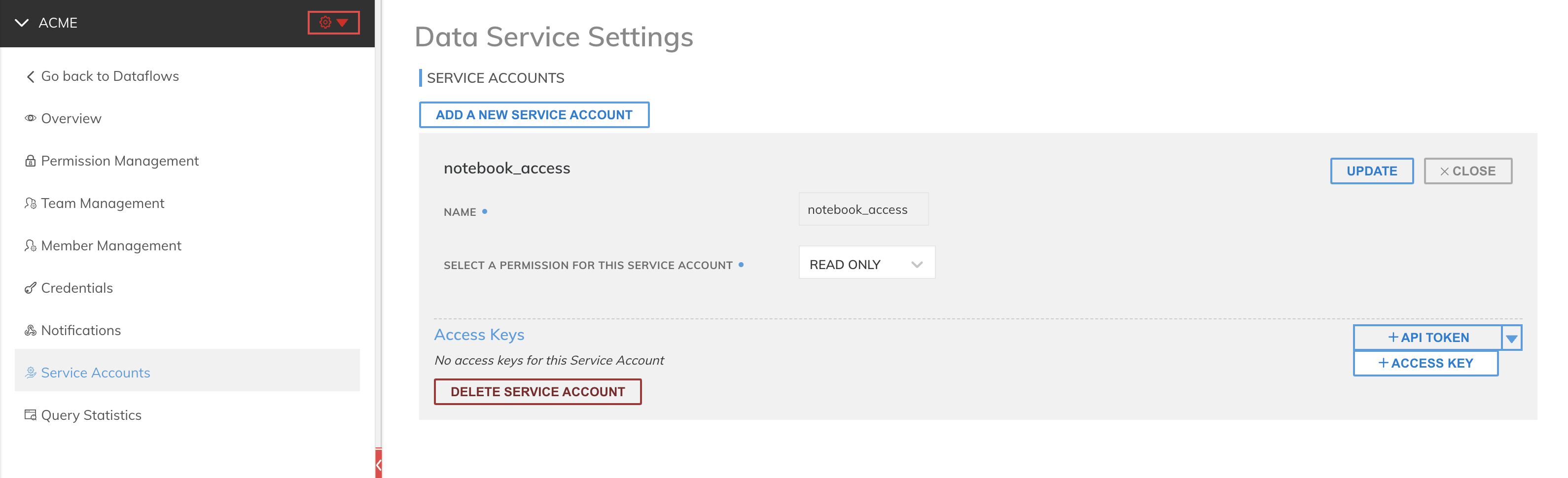
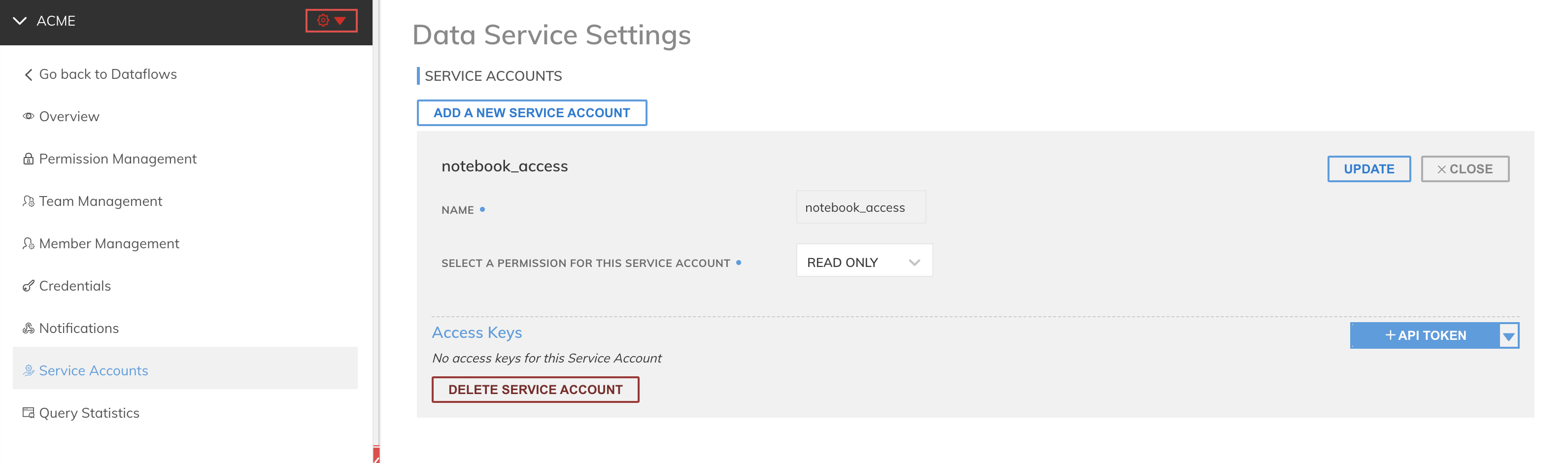
Create Access Key with "API Token" Credential Type
- In the Service Accounts tab, click the + API TOKEN button in the drop-down
- A pop-up window displaying the API Token will be presented. This is the only opportunity to copy the secret key. You may, however, create new keys at any time.
Updated 11 months ago